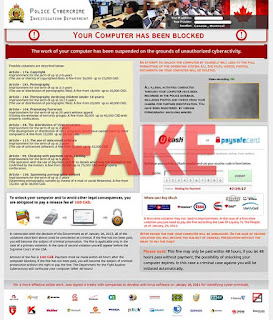
Police Cybercrime Investigation Department warning you see at the image below is a contemporary form of a serious virus infection that targets computers located in Canada (possibly some other countries as well). This is the scam that is classified as ransomware, i.e. the program that hijacks the attacked workstation, locks the screen and accuses users of performing various crimes online. Then the warning says that users must pay the fine to have the workstation unblocked. Of course, you should not ever do as instructed by this scary warning, because the authors of this alert are the crooks who want to become richer through deceiving simple users today.
It should be noted that Police Cybercrime Investigation Department, of course, is not associated with this scam. The warning that says that your computer has been blocked and that the work of your computer has been suspended on the grounds of unauthorized cyber activity is elaborated by the pack of cyber frauds. However, the fake accusations contained in the text of the ransomware locker are surely scary for all users. The malware condemns users of performing the following crimes:
- Violation of copyrights
- Distribution of pornography
- Distribution of pornography involving children (under 18 years
- Promoting terrorism
- Distribution of virus programs
- The use of unlicensed software
- Cheating with payment cards, carding
- Spamming pornographic content
When you get such a scary alert supposedly coming from Police Cybercrime Investigation Department please disregard its contents completely! Remember that you should search for the correct solution that will help you unlock your system. Hackers don’t guarantee that the PC will be unlocked after users pay this ransom, so under no circumstances should you obey their instructions. It should be also mentioned that if you reboot the computer several times the locked condition of it will remain. You need to implement some manual steps that will be helpful and effective enough to unblock your system. Please find these guidelines stipulated below.
Screenshot of Police Cybercrime Investigation Department virus:
Automatic removal solution (recommended):
- Go to your friend, relative or anybody else who has computer with Internet connection.
- Take your USB flash drive / Memory Stick with you.
- Download GridinSoft Trojan Killer installation file from this site http://trojan-killer.net/download.php and save it to your USB flash drive / Memory Stick.
- Get back to your infected PC and insert the USB Drive / Memory Stick into the respective USB slot.
- Perform hard reset (press reset button on your computer) if your infected PC has been on with ransomware's background. If not, then simply turn your PC on.
- Before the very boot process begins keep repeatedly hitting “F8” button on your keyboard.
- In the window that appeared select “Safe mode with command prompt” option and press Enter.
- Choose your operating system and user account which was infected with ransomware virus.
- In the cmd.exe window type “explorer” and press “Enter” button on your keyboard.
- Select “My Computer” and choose your USB flash drive / Memory Stick.
- Run the installation file of GridinSoft Trojan Killer. Install the program and run scan with it. (update of the program will not work for “Safe mode with command prompt” option)
- When the hijackers are successfully disabled (fixed) by GridinSoft Trojan Killer you may close GridinSoft Trojan Killer application.
- In the cmd.exe window type “shutdown /r /t 0” and press “Enter” button on your keyboard.
- Upon system reboot your PC will be unlocked and you will be able to use it just as before the infection took pace.
- However, it is recommended that you now update GridinSoft Trojan Killer and run the scan with it again to remove the source of the infections causing ransomware to infect your PC.
Automatic removal video:
Ransomware manual removal milestones (optional and might not be effective):
- Restart your system into "Safe Mode with Command Prompt". While the PC is booting press the "F8 key" continuously, which should present the "Windows Advanced Options Menu" as presented in the image below. Apply the arrow keys in order to move to "Safe Mode with Command Prompt" and hit Enter key of your keyboard. Login as the same user you were previously logged in under the normal Windows mode.
- Once Windows boots successfully, the Windows command prompt would appear as described at the screenshot below. At the command prompt, type-in the word "explorer", and press Enter. Windows Explorer should open. Please do not yet close it. You can minimize it for a while.
- Afterwards open the Registry editor by applying the same Windows command prompt. Type-in the word "regedit" and hit Enter button of your keyboard. The Registry Editor should open.
- Find the following registry entry:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\In the right-side panel select the registry entry named Shell. Right click on this registry key and select "Modify" option. Its default value should be "Explorer.exe". However, ransomware did its job, and so after you click "Modify" you would see totally different value of this registry entry. - Copy the location of the modified value of the above-mentioned registry entry to the piece of paper or memorize its location. It shows where exactly the main executable of ransomware is located.
- Modify the value of the registry entry back to "explorer.exe" and save the settings of the Registry Editor.
- Go to the location indicated in the value of modified registry entry. Remove the malicous file. Use the file location you copied into the piece of paper or otherwise noted in step in previous step. In our case, ransomware's virus file was located and running from the Desktop. There was a file called "contacts.exe", but it may have different (random) name.
- Get back to "Normal Mode". In order to reboot your PC, when at the command prompt, type-in the following phrase "shutdown /r /t 0" (without the quotation marks) and hit Enter button.
- The virus should be gone. However, in order to clean your PC from other possible virus threats and malware remnants, make sure to download and run GridinSoft Trojan Killer downloadable through the button below.
Manual removal video:
Associated virus files to be removed:
[random].exe Associated virus registry entries to be removed:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\"Shell" = "[random].exe"

No comments:
Post a Comment