El virus de Policia Federal Argentina es un programa ransomware que muestra una advertencia del mensaje falsa sobre un poco de delito criminal. El programa bloquea el sistema apuntado completamente y no permite realizar algo allí. Sólo muestra un mensaje diciendo que se ha implicado en la distribución del contenido pornográfico y por esta razón debe pagar una multa.
Como ve, el mensaje viene a la lengua española un principalmente ordenadores de ataques localizados en Argentina. Hasta usa un nombre de Argentina Federal Police aunque no tenga nada que ver con esta institución. El mensaje menciona un manojo de artículos de la ley que supuestamente se rompió y le dice pagar una multa de 200 ARS. A la multa le piden pagarse vía el sistema del pago de Ukash que lo hace muy fácil para los criminales ciber conseguir su dinero en seguida. Aquí está cómo el mensaje parece citado abajo.
Policia Federal Argentina entra en vulnerabilidades del sistema de utilización de ordenadores, vía virus troyanos por tanto el usuario de ordenador no puede ver esta infiltración. ¡Precávase de esta timo! Quite el virus de Policia Federal Argentina de su ordenador sin cualquier duda. La policía nunca usaría tales medios de informarle sobre violaciones de la ley. El programa bloqueará cada solo programa en su ordenador así como gerente de la Tarea que complicará el retiro del virus mal. Recomendamos después de estas instrucciones de retiro debajo de las cuales explican cómo eliminar este tipo de programas ransomware de unos modos diferentes.
Screenshot of Policia Federal Argentina virus:
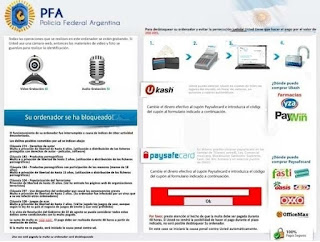
Quotation from fake Policia Federal Argentina scary alert:
PFA
Policia Federal Argentina
Su ordenador se ha bloqueado!
El funcionamiento de su ordenador fue interrumpido a causa de indices de ciberactividad desautorizada.
Los delitos posibles cometidos por Lid se indican abajo.
Cláusula 274— Derechos de autor Multa o privación de libertad de hasta 4 anos. (utilización o distribuición de los ficheros protegidos con derechos de autor — peliculas, software]
Cláusula 183 — Productos pornográficos Multa o o privación de libertad de hasta 2 anos. (Utilización o distribuición de los ficheros pornográficos)
Cláusula 1E4 — Productos pornográficos con participación de los menores (menos de 18 anos) Multa o privación de libertad de hasta 1$ anos.
Automatic removal solution (recommended):
- Go to your friend, relative or anybody else who has computer with Internet connection.
- Take your USB flash drive / Memory Stick with you.
- Download GridinSoft Trojan Killer installation file from this site http://trojan-killer.net/download.php and save it to your USB flash drive / Memory Stick.
- Get back to your infected PC and insert the USB Drive / Memory Stick into the respective USB slot.
- Perform hard reset (press reset button on your computer) if your infected PC has been on with ransomware's background. If not, then simply turn your PC on.
- Before the very boot process begins keep repeatedly hitting “F8” button on your keyboard.
- In the window that appeared select “Safe mode with command prompt” option and press Enter.
- Choose your operating system and user account which was infected with ransomware virus.
- In the cmd.exe window type “explorer” and press “Enter” button on your keyboard.
- Select “My Computer” and choose your USB flash drive / Memory Stick.
- Run the installation file of GridinSoft Trojan Killer. Install the program and run scan with it. (update of the program will not work for “Safe mode with command prompt” option)
- When the hijackers are successfully disabled (fixed) by GridinSoft Trojan Killer you may close GridinSoft Trojan Killer application.
- In the cmd.exe window type “shutdown /r /t 0” and press “Enter” button on your keyboard.
- Upon system reboot your PC will be unlocked and you will be able to use it just as before the infection took pace.
- However, it is recommended that you now update GridinSoft Trojan Killer and run the scan with it again to remove the source of the infections causing ransomware to infect your PC.
Automatic removal video:
Ransomware manual removal milestones (optional and might not be effective):
- Restart your system into "Safe Mode with Command Prompt". While the PC is booting press the "F8 key" continuously, which should present the "Windows Advanced Options Menu" as presented in the image below. Apply the arrow keys in order to move to "Safe Mode with Command Prompt" and hit Enter key of your keyboard. Login as the same user you were previously logged in under the normal Windows mode.
- Once Windows boots successfully, the Windows command prompt would appear as described at the screenshot below. At the command prompt, type-in the word "explorer", and press Enter. Windows Explorer should open. Please do not yet close it. You can minimize it for a while.
- Afterwards open the Registry editor by applying the same Windows command prompt. Type-in the word "regedit" and hit Enter button of your keyboard. The Registry Editor should open.
- Find the following registry entry:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\In the right-side panel select the registry entry named Shell. Right click on this registry key and select "Modify" option. Its default value should be "Explorer.exe". However, ransomware did its job, and so after you click "Modify" you would see totally different value of this registry entry. - Copy the location of the modified value of the above-mentioned registry entry to the piece of paper or memorize its location. It shows where exactly the main executable of ransomware is located.
- Modify the value of the registry entry back to "explorer.exe" and save the settings of the Registry Editor.
- Go to the location indicated in the value of modified registry entry. Remove the malicous file. Use the file location you copied into the piece of paper or otherwise noted in step in previous step. In our case, ransomware's virus file was located and running from the Desktop. There was a file called "contacts.exe", but it may have different (random) name.
- Get back to "Normal Mode". In order to reboot your PC, when at the command prompt, type-in the following phrase "shutdown /r /t 0" (without the quotation marks) and hit Enter button.
- The virus should be gone. However, in order to clean your PC from other possible virus threats and malware remnants, make sure to download and run GridinSoft Trojan Killer downloadable through the button below.
Manual removal video:
Associated virus files to be removed:
[random].exe Associated virus registry entries to be removed:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\"Shell" = "[random].exe"

No comments:
Post a Comment